Cybersecurity Monthly Report (February2026)
Cybersecurity Monthly Report (February2026)
1. Recent Cybersecurity Incident Sharing
Service Performance Degradation Due to Database Connection Pool Exhaustion
A governing authority's shared system, utilized by personnel across all levels of government, suffered a degradation in service performance that caused significant user-side delays during login and operations. Investigation revealed that query optimization failed to keep pace with continuous post-launch data growth, leading to excessive execution times and the exhaustion of database connections. Under high concurrent loads, the database connection pool became entirely depleted, severely degrading system performance. The agency promptly coordinated with the maintenance vendor to scale up the connection limit while mobilizing personnel for emergency query optimization. These measures effectively mitigated service latency and restored normal operations.
Lessons Learned
As data volume and user demand continue to grow over time, failure to keep system performance design aligned with these changes may reduce resource efficiency and affect overall service stability. Agencies are advised to establish continuous performance monitoring and periodic review mechanisms after system deployment, conduct regular capacity and performance assessments, incorporate performance testing into operation and maintenance processes, and synchronize performance design reviews with system changes:
(1) Establish continuous performance monitoring mechanism
After system deployment, a continuous performance monitoring mechanism should be established to track service performance and resource utilization, including login response time, connection pool utilization, and overall system load. Alert thresholds should be configured to detect early signs of performance degradation and prevent accumulated issues from affecting service operations.
(2) Regular Capacity and Performance Assessment
As the number of users and data volume continue to grow, system capacity and resource allocation should be regularly evaluated. For example, peak login volumes and data growth trends should be reviewed, and stress testing should be conducted to simulate higher usage scenarios (e.g., 2x increase in concurrent user load) to ensure that the system can handle the increased load and prevent service congestion during peak periods.
(3) Incorporate performance testing into operation and maintenance processes
For example, regularly review slow queries and optimize performance, or establish performance checklists as mandatory pre-deployment procedures.
(4) Synchronize performance design reviews with system changes
When new functions are added, system upgrades are performed, or data volume increases, data access and query methods should be reviewed. For example, avoid loading excessive historical data at once, adopt pagination mechanisms, or create database indexes as needed to improve query efficiency.
2. Cybersecurity Trends
2.1 National Government Cybersecurity Threat Trends
Ex ante joint defense and monitoring
This month, a total of 60,764 cybersecurity joint defense intelligence items were collected from government agencies, (a decrease of 11,979 items). Among identifiable threat categories, information collection ranked first (54%), primarily involving the acquisition of information through techniques such as scanning, probing and social engineering. This was followed by intrusion attempts (18%), mainly involving attempts to access unauthorized hosts, and intrusion attacks (15%), most of which involved unauthorized system access or the acquisition of system or user privileges. The distribution of intelligence volume over the past year is shown in Figure 1.
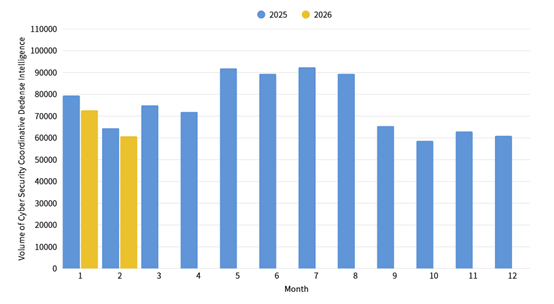
Figure 1: Statistics of cybersecurity monitoring intelligence in joint defense
Cybersecurity Alert: Phishing Campaign Impersonating the Executive Yuan’s Legal Affairs Committee
Following the compilation and analysis of joint defense intelligence, it was recently discovered that attackers have launched social engineering email campaigns impersonating the Legal Affairs Committee of the Executive Yuan. Using the amendment to Article 5 of the “Regulations for Revenues, Expenditures, Safeguard and Utilization of the Employment Security Fund” as a pretext, these campaigns targeted government agencies and state-owned enterprises. The attackers leveraged compromised private enterprise domains and spoofed Executive Yuan sender accounts (executive-yuan). Both the sender’s name and email content were crafted to mimic the “Legal Affairs Committee of the Executive Yuan” to enhance credibility. Recipients were induced to click phishing links and download malicious attachments under the guise of reviewing purported “amended articles”. This resulted in the installation of a malicious backdoor program (Cobalt Strike), granting attackers remote control over compromised systems. Relevant intelligence and defensive recommendations have been provided to government agencies for joint monitoring and protection.
In-Process Reporting and Responding
This month, a total of 54 reported cybersecurity incidents were recorded, representing 90% of the volume from the same period last year. The majority of reported incidents were categorized as illegal intrusions, accounting for 72.22% of the total. In addition to the detection of suspected PeerBlight malware distribution via routers, multiple agencies were infected with malware stemming from the installation of counterfeit software, accounting for 25.93% of the total reported cases. Statistics for cybersecurity incident reports over the past year are illustrated in Figure 2.
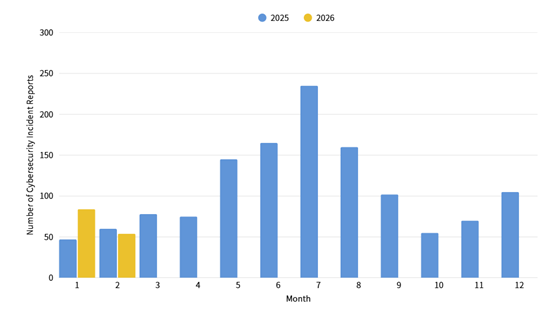
Figure 2: Statistics of cybersecurity incident reports
3.2 Important Vulnerability Alerts
| Alert Type | Category | Description |
|---|---|---|
| Vulnerability Alert |
Directory Service |
|
| Email System C&Cm@il Collaborative Mail System Severity: (CVE-2026-2234: CVSS 9.1), (CVE-2026-2235: CVSS 6.5), and (CVE-2026-2236: CVSS 7.5) |
|
|
| Process Management System AgentFlow Severity: (CVE-2026-2095: CVSS 9.8), (CVE-2026-2096: CVSS 9.8), (CVE-2026-2097: CVSS 8.8), (CVE-2026-2098: CVSS 6.1), (CVE-2026-2099: CVSS 5.4) |
|
|
| Known Exploited Vulnerability |
Communication Equipment |
|
|
Office Software |
|
|
|
Web Browser |
|
|
|
Network Security Equipment: |
|
Alert Explanations:
Vulnerability Alert: Verified vulnerabilities that have not yet been widely exploited by attackers. It is recommended to arrange updates as soon as possible.
Known Exploited Vulnerability: Known instances of successful attacks exploiting the vulnerability. Immediate evaluation and patching are strongly recommended.
3. International Cybersecurity News
Attackers Use Fake PDF Lures to Steal Dropbox Login Credentials (Source: Dark Reading)
According to a research report by Forcepoint, phishing attacks targeting enterprises are on the rise recently. Attackers have adopted sophisticated multi-stage obfuscation techniques in an attempt to trick victims into entering and surrendering their Dropbox account credentials. In this attack campaign, attackers send emails from spoofed or compromised internal email accounts to lure target users into viewing a fake “purchase order request.” The email contains a link to a PDF document. When users click the link, they are first redirected to an obfuscated PDF file hosted on the legitimate cloud service platform Vercel, and are then redirected again to a fake Dropbox login page that closely resembles the official one. On that page, victims are prompted to enter their work account credentials. In fact, those credentials are stolen by the attackers before the page displays an “incorrect username or password” message. The stolen credentials and related user information are then exfiltrated in real time to the attackers via a Telegram bot, enabling further account takeover, internal system access, and even follow-on fraud. To reduce the risk of such attacks, users are advised to follow phishing prevention best practices, such as remaining vigilant against emails and PDF attachments from unknown sources, and carefully verifying the authenticity of links before opening or clicking them.
Microsoft: Critical Windows Admin Center Vulnerability Enables Privilege Escalation (Source: Tech Republic)
Microsoft has issued a warning regarding a high-risk vulnerability (CVE-2026-26119, CVSS score: 8.8) in Windows Admin Center (WAC), which could be exploited in enterprise environments to conduct privilege escalation attacks. The vulnerability stems from improper handling of authentication mechanisms, allowing attackers with legitimate access to elevate their privileges over the network without requiring user interaction.
If successfully exploited, attackers could obtain administrative-level control, enabling them to modify system configurations, create or alter privileged accounts, disable security protections, access sensitive data, and even perform lateral movement within enterprise networks. As Windows Admin Center is a centralized management platform for servers and infrastructure, exploitation of this vulnerability could impact multiple managed hosts and further amplify overall security risks.
The vulnerability affects Windows Admin Center version 2.6.4. As of now, there is no evidence of exploitation in the wild. Organizations are advised to mitigate risks by applying the latest patches, enforcing the principle of least privilege, implementing multi-factor authentication, restricting network exposure, hardening host systems, enabling enhanced logging, and testing incident response plans.