Cybersecurity Monthly Report (January 2026)
Cybersecurity Monthly Report (January 2026)
1. Policy Highlights
In alignment with the amendment to the Cyber Security Management Act, four subordinate regulations, namely (Tentative) the Enforcement Rules of Cyber Security Management Act, the Regulations on Audit of Implementation of Cyber Security Maintenance Plan, the Regulations on Cyber Security Incident Notification and Response and Exercises, and the Cyber Security Information Sharing Regulations, were amended and came into effect on January 7, 2026. The Regulations on Classification of Cyber Security Responsibility Levels was amended and implemented on January 9, 2026. The Regulations Governing the Handling of Cyber Security Matters of Government Agency Personnel was amended and implemented on January 15, 2026.
2. Recent Cybersecurity Incident Sharing
Malicious Commands Embedded in External Website Lead to Plaintext Data Exfiltration
During official duties, agency personnel accessed an external corporate website that had been compromised by attackers. Malicious scripts were implanted on the website, automatically redirecting users to additional malicious sites upon browsing. This subsequently triggered background downloads of malicious programs and induced users to installation and execution. After execution, the malware packaged and transmitted data from the affected computer to intermediary servers, resulting in information leakage.
Lessons Learned
In this incident, attackers manipulated website scripts to induce users to download and install malicious programs. This highlights the need to strengthen endpoint protection mechanisms, particularly in detecting and blocking abnormal command signatures, unauthorized program loading, and suspicious behavioral activities. To prevent similar incidents, the following defensive measures are recommended:
(1) Application Download and Installation Controls
Establish governance mechanisms for application downloads and installations. Such activities should be regulated through internal management policies, and user cybersecurity awareness should be enhanced to prevent downloading unknown or suspicious programs.
(2) Implementation of Endpoint Detection and Response (EDR)
Continuously monitor endpoint devices for suspicious behavior, promptly detect signs of malicious activities, and reduce the risk of subsequent cybersecurity incidents.
3. Cybersecurity Trends
3.1 National Government Cybersecurity Threat Trends
Ex ante joint defense and monitoring
This month, a total of 72,743 cybersecurity joint defense intelligence items were collected from government agencies (an increase of 11,163 items). Among identifiable threat categories, information collection ranked first (41%), primarily involving scanning, probing, and social engineering techniques. This was followed by intrusion attempts (24%), mainly involving attempts to intrude into unauthorized hosts, and intrusion attacks (17%), most of which involved unauthorized system access or the acquisition of system or user privileges. Statistics on the distribution of intelligence over the past year are shown in Figure 1.
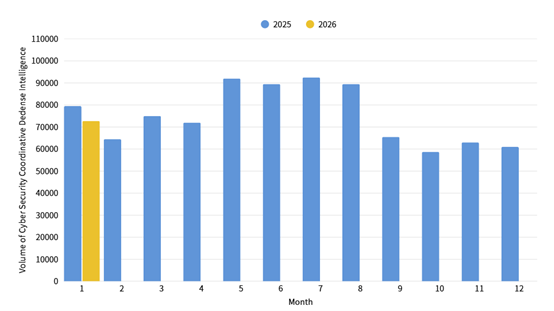
Figure 1: Statistics of cybersecurity monitoring intelligence in joint defense
Social Engineering Email Attacks Impersonating Administrative Litigation Notices
After further compilation and analysis of joint defense intelligence information, it was recently discovered that attackers have launched social engineering email campaigns targeting government agencies using “administrative litigation” as a lure. The sender display name was labeled as “Administrative Litigation Complaint” to create a false sense of legal authority and urgency, thereby increasing the likelihood of recipients opening the email. The subject lines deliberately included the recipient agency’s name, and the email content was disguised as an official court notice containing seemingly legitimate information such as case numbers and case titles to enhance credibility. Recipients were induced to click embedded links to view so-called “related materials”, which resulted in the download and installation of a malicious backdoor program (ValleyRAT) for the purpose of exfiltrating sensitive data from compromised systems. Relevant intelligence and defensive recommendations have been provided to government agencies for joint monitoring and protection.
In-Process Reporting and Responding
A total of 84 cybersecurity incident reports were received this month, representing 1.79 times the number reported during the same period last year. The primary category of incidents was illegal intrusion, accounting for 66.67% of the total reports. Notably, the most frequently reported incidents involved the installation of counterfeit software leading to malware infection, accounting for 16.67% of total reported cases. Statistics for cybersecurity incident reports over the past year are shown in Figure 2.
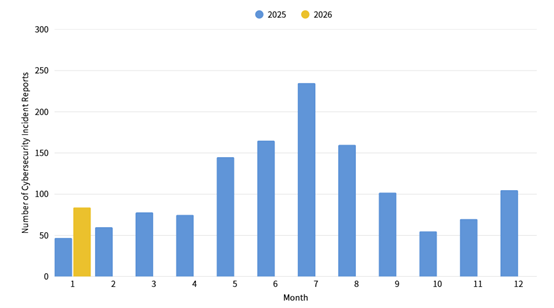
Figure 2: Statistics of cybersecurity incident reports
3.2 Important Vulnerability Alerts
| Alert Type | Category | Description |
|---|---|---|
| Vulnerability Alert |
Surveillance Cameras: Lilin NVRs and IP Cameras |
|
| Application QNAP NAS Severity: CVSS 8.1 (CVE-2025-59384 CVE-2025-59387) |
|
|
| Centralized Management Platform: Trend Micro Apex Central Severity: CVSS 9.8 (CVE-2025-69258) |
|
|
| Known Exploited Vulnerability |
Email Management System: Cisco AsyncOS Software |
|
|
Unified Communications: Cisco Unified Communications |
|
Alert Explanations:
Vulnerability Alert: Verified vulnerabilities that have not yet been widely exploited by attackers. It is recommended to arrange updates as soon as possible.
Known Exploited Vulnerability: Known instances of successful attacks exploiting the vulnerability. Immediate evaluation and patching are strongly recommended.
4. International Cybersecurity News
Dozens of Chrome Extensions Hacked, Exposing Millions of Users to Data Theft (Source: The Hacker News)
A new attack campaign has targeted known Chrome browser extensions, leading to at least 35 extensions being compromised and exposing over 2.6 million users to data exposure and credential theft. The attack targeted publishers of browser extensions on the Chrome Web Store via a phishing campaign and used their access permissions to insert malicious code into legitimate extensions in order to steal cookies and user access tokens. On December 27, 2025, cybersecurity firm Cyberhaven disclosed that attackers had compromised its browser extension and injected malicious code that communicated with external command-and-control (C2) servers, downloaded additional configuration files, and exfiltrated user data. The phishing email used in the campaign was disguised as a message from the Google Chrome Web Store Developer Support team. It falsely claimed that the extension was at risk of removal due to violations of developer policies, thereby creating a sense of urgency. Victims were redirected to an authorization page and tricked into granting permissions to a malicious OAuth application.
Widely Used Malicious Extensions Steal ChatGPT, DeepSeek Conversations (Source: Security Boulevard)
Researchers from OX Security discovered two malicious browser extensions disguised as legitimate tools that were used to steal users’ browsing data as well as their conversations with AI models such as ChatGPT and DeepSeek. The two extensions were “Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AI” (with more than 600,000 users) and “AI Sidebar with DeepSeek, ChatGPT, Claude and more” (with more than 300,000 users).
These extensions reportedly transmitted sensitive information to remote command-and-control (C2) servers every 30 minutes, including proprietary source code, business strategies, personally identifiable information (PII), confidential corporate communications, full Chrome tab URLs, and search queries.
Attackers impersonated a legitimate sidebar extension developed by AITOPIA, leveraging its extensive permissions to monitor and extract sensitive data in real time. If a user removed one extension, the malware prompted the installation of another extension, allowing it to maintain persistence.
OX Security notified Google about the malicious extensions on December 29, 2025, and Google responded on December 30 that the issue was under review.
Critical jsPDF flaw lets hackers steal secrets via generated PDFs
(Source: Bleeping Computer)
A critical vulnerability tracked as CVE-2025-68428 (CVSS: 9.2) has been discovered in jsPDF, a library used for generating PDF documents in JavaScript applications. The vulnerability could allow attackers to steal sensitive data from local file systems by embedding local file contents into generated PDF documents. The vulnerability exploits local file inclusion and path traversal issues, allowing unfiltered paths to be passed to the loadFile method in versions prior to jsPDF 4.0. When user-controlled input is supplied as a file path, jsPDF may incorporate the contents of the specified file into the generated PDF output. Other file-loading methods are also affected, including addImage, html, and addFont.
The vulnerability was fixed in jsPDF version 4.0, which restricts file system access by default and relies on the Node.js permission model to strengthen security. However, researchers from Endor Labs noted that the permission model remains experimental in Node 20. They therefore recommend using Node versions 22.13.0, 23.5.0, or 24.0.0 and later.
5. Recent Key Cybersecurity Meetings and Activities
| Date | Event/Meeting | Audience |
|---|---|---|
|
February 9-12, 2026 |
Intensive Practical Training for the Cybersecurity Category in the Civil Service Level 3 Senior Examination |
Admitted Personnel in Cybersecurity Category |